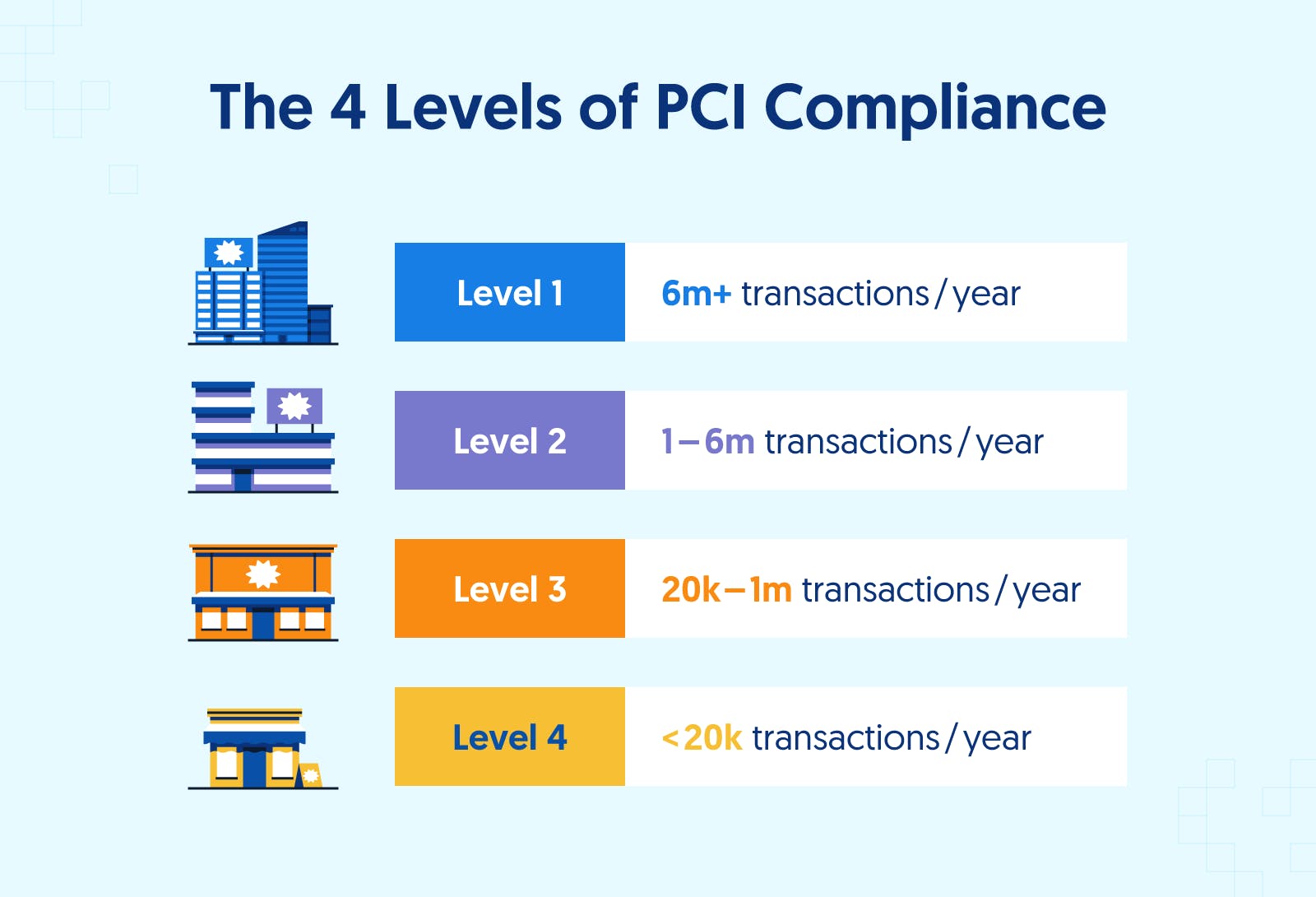
Merchant levels and Compliance Validation Requirements
| PCI Merchant Levels | ||
| Level | Description | Validation Requirements |
| 1 |
|
|
| 2 |
|
|
| 3 |
|
|
| 4 |
|
|
Merchant Types
The “SAQ” is a self-validation tool for merchants and service providers who are not required to do on-site assessments for PCI DSS compliance. The SAQ includes a series of yes-or-no questions for compliance. If an answer is no, the organization must state the future remediation date and associated actions. In order to align more closely with merchants and their compliance validation process, the SAQ was revised and now allows for flexibility based on the complexity of a particular merchant’s or service provider’s business situation (see chart below). The SAQ validation type does not correlate to the merchant classification or risk level.
| Self-Assessment Questionnaires and Validation Types | ||
| SAQ ValidationType | Description | SAQ |
| 1 | Card-Not-Present (e-commerce or MO/TO) merchants, all cardholder data functions outsourced. This would never apply to face-to-face merchants. |
A |
| 2 | Imprint-only merchants with no cardholder data storage. | B |
| 3 | Standalone dial-up terminal merchants, no cardholder data storage. | B |
| 4 | Merchants with payment application systems connected to the Internet, no cardholder data storage. |
C |
| 5 | All other merchants (not included in descriptions for SAQs A, B or C above), and all service providers defined by a card brand as eligible to complete a SAQ. |
D |
Service Provider Levels
Service providers are organizations that process, store, or transmit cardholder data on behalf of clients, merchants, or other service providers. Service provider levels are defined as:
| Self-Assessment Questionnaires and Validation Types | ||
| Service Provider Level | Description | Validation Requirements |
| 1 | Processors or any service providers that stores, processes and/or transmits over 300,000 transactions per year. |
|
| 2 | Any service provider that stores, processes and/or transmits less than 300,000 transactions per year. |
|
By using the charts above, you should be able to easily determine your level and validation type. Knowing this details will go a long way in guiding you through your compliance but it is important to partner with other qualified businesses for your service. ZZ Servers provides PCI focused hosted infrastructure designed for PCI compliance and includes many of controls and measures required for your business infrastructure to be fully compliant.