
A Guide to Common Types of Foundational System Software
To answer the question “What are examples of system software?” this guide provides a comprehensive overview of common types of foundational programs used in computers

To answer the question “What are examples of system software?” this guide provides a comprehensive overview of common types of foundational programs used in computers

In today’s digital age, technology has become interwoven into business fabric. Companies rely heavily on IT systems, from large enterprises to small startups, to carry

Application security is the tactics and practices to protect software applications from threats and holes. Many methods, tools, and processes ensure that an application and

Uncover the differences between IT Consulting and IT Services. Learn how to make the best decision for your business needs.

Unlock the potential of outsourcing IT services: Evaluate the pros and cons to get the most out of it!

Discover top 7 benefits of outsourcing IT services. Boost efficiency and save money with these 7 benefits. Click now to learn more!
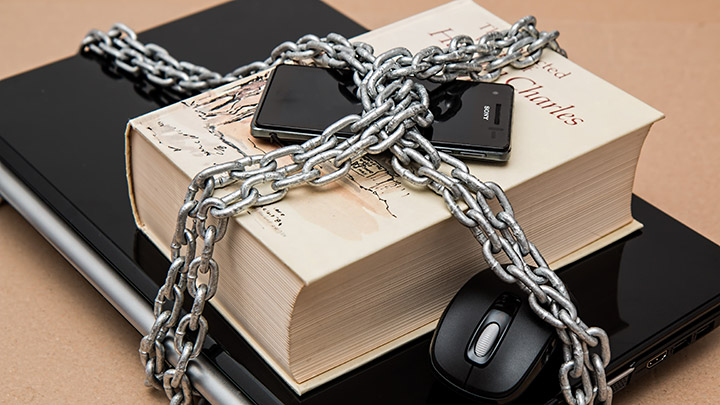
Discover the power of data security tools to protect your information—find out what they are and how to use them.

Discover the ultimate toolkit for tackling cyber threats! Unleash the power of threat intelligence tools and fortify your defense strategy today.

Learn about the main types of cybersecurity solutions, including network security, cloud security, endpoint protection, and more, to secure your business.

Learn about the most common cybersecurity risks like malware, data breaches, phishing, and ransomware so you can protect your business with the right solutions.
We’re happy to answer any questions you may have and help you determine which of our services best fit your needs.
We Schedule a call at your convenience
We do a discovery and consulting meting
We prepare a proposal