It amazes me that I still sometimes hear people talking about cybersecurity (logical security) and physical security as if they’re separate issues to address and manage. Today, in our connected world, that’s not the case at all. Our digital world has produced a convergence of physical and logical security that brings value to how you protect your most valuable assets, both in business and at home.
First Things First
You absolutely need both. You wouldn’t protect your computer from malware and not lock the front door of your house. And on a business level, you can’t address PCI compliance, by simply encrypting cardholder data, setting up secure systems and controlling digital access to data. You also must protect access the physical components containing cardholder data such as storage media, point-of-sale devices, laptops, data centers, and buildings and rooms that contain cardholder data, etc.
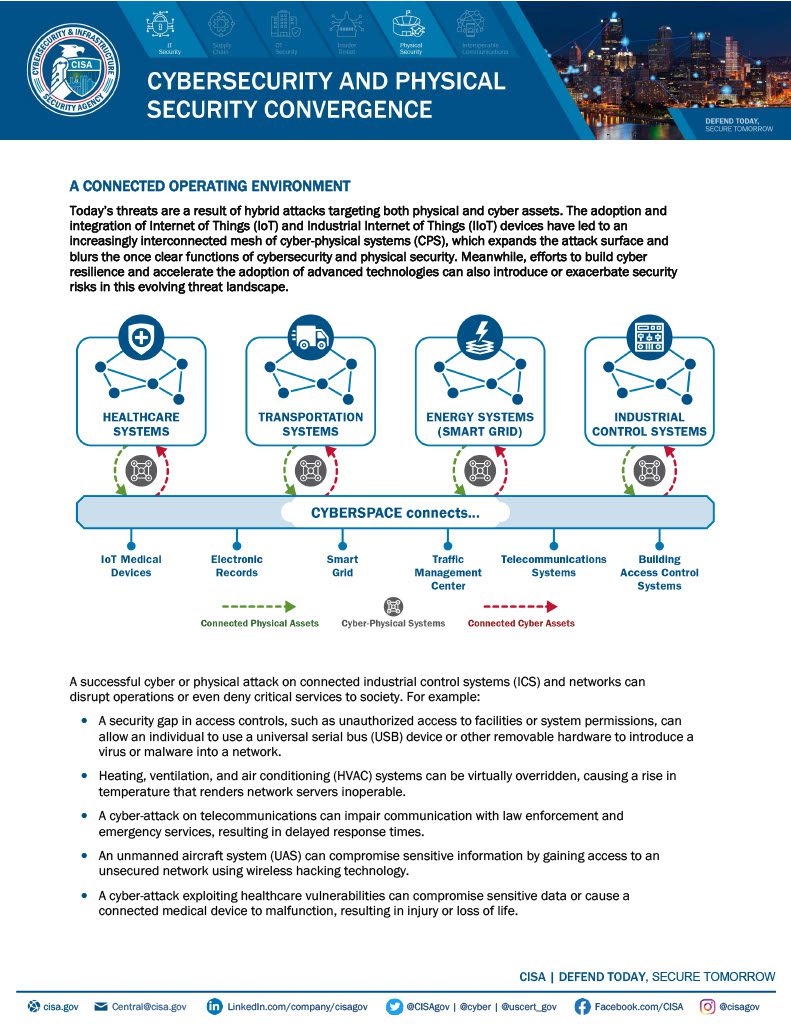
Over time, it became clear that linking physical security with logical security was the way forward, whether we’re talking about the Ring phenomena, which essentially turned the doorbell into an Internet of Things, WiFi home security system, or the badge system to get into an office or building.Linking logical with physical offered businesses several opportunities for added value in the areas of reduced risk, improved efficiencies and reduced operational costs.
Where’s the Value?
A starting point for any security strategy designed to reduce risk is a risk assessment, which ultimately identifies the most important assets that need to be protected and where they are located. For example, if you’re a business that has cardholder data to protect, one element of your security system must be controlling access to the data at both the physical and logical level. To address this, you can incorporate multi-factor authentication which means to access the data and the resources it’s stored on, you must have something – such as a badge to enter the building and the data center itself. You also must have something you know – such as a password that grants access to the network holding the cardholder data.
This blend of physical and logical security greatly reduces risk of data loss by strongly controlling access to the information on multiple levels with a single system.
The convergence of physical and logical security also can greatly improve operational efficiencies. One of the best examples of this is the provisioning and deprovisioning process for employees. With single source of truth to manage identities, employees can get everything they need to be productive for the business quickly – whether it’s a badge for building access or access and authorization to use various applications and IT systems within the company. More importantly, when there is a termination or a change in roles, that employee’s access can be revoked or changed quickly to help ensure security of both the physical and the digital / logical assets.
Finally, operational costs can be streamlined when physical and logical security blend. For example, security operations teams can be cross-trained and duties shared; it’s easier to negotiate budgets and have a holistic view of short-term needs and what could be moved to the next budgeting round; and information sharing can improve insight for a “big picture” view that could be more informative and telling than if the physical and logical systems were siloed.
If you examine your security initiatives, you’re sure to see a convergence of physical and logical. Take a closer look and assess what you’re doing to make sure you’re getting all the value you can from where you’ve blended security. Questions? Need a consultation? Contact us.